UEFI vs BIOS: Building a Better Firmware
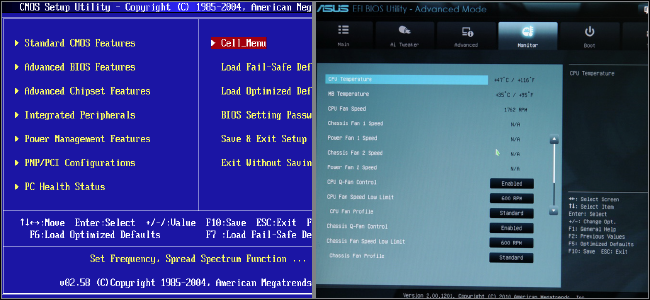
Before the release of UEFI (Unified Extensible Firmware Interface) in 2007, the basic input/output system (BIOS) has been the main fixture in personal computers since the 1970s. What is the difference between UEFI vs BIOS?
What is BIOS?
Packed into silicon on the PC motherboard, the BIOS detects and initializes devices at startup and accesses the master boot record (MBR) on the hard drive to start the boot process. The BIOS also serves as an important, low-level management tool, allowing admins to tweak system behavior, implement security, and control peripheral devices and storage.
Over time, PCs have outgrown the traditional BIOS, with its scant 1MB memory ceiling and 16-bit architecture that limits boot drive capacities to 2.1TB.
What is UEFI?
In 2007, a consortium of companies including Intel, AMD, Microsoft, and key PC manufacturers crafted an advanced successor to the BIOS, managed by the Unified Extensible Firmware Interface Forum.
PC makers have largely transitioned to UEFI. However, many organizations continue to manage a mix of UEFI-based PCs and older BIOS-based computers. The term “BIOS” is also still commonly used to refer to both BIOS and UEFI architectures.
UEFI vs BIOS – Key Differences
UEFI is more than just an expanded BIOS with graphical elements, a mouseable UI, and support for 32 and 64-bit code. It enables new levels of security and robustness at the foundation of the compute architecture. UEFI also establishes a “root of trust” upon which all other security solutions, such as anti-malware software, can rely.
Case in point is the UEFI Secure Boot feature. This feature employs digital signatures to verify the integrity of low-level code like boot loaders and operating system files before execution. If validation fails, Secure Boot halts execution of the compromised bits to stop any potential attack in its tracks. This scheme can blunt the most pernicious threats such as hard-to-detect rootkits that can otherwise elude detection and remediation. Note that this Secure Boot feature is a required feature for Windows 11.
Another important benefit of UEFI is that it does not rely on the fragile Master Boot Record (MBR) scheme to store the low-level bits that bootstrap the operating system. Under MBR, these key bits reside in the first segment of the disk, and any corruption or damage to that area prevents the operating system from loading. By contrast, UEFI employs the GUID Partition Table (GPT) scheme and stores initialization code in an .efi file found in a hidden partition. GPT also stores redundant copies of this code and uses cyclic redundancy checks to detect changes or corruption of the data. The result is a far more robust and recoverable boot environment for UEFI-based PCs.
UEFI vs BIOS: Comparison Chart
| BIOS | UEFI | |
| Established | 1975 | 2007 |
| Architecture | 16-bit | 32-bit/64-bit |
| Boot drive capacity | 2.1TB | 9.4ZB (9.4 billion terabytes) |
| Partitioning scheme | MBR | GPT |
| Program language | Assembly | C |
| Primary partition limit | 4 | No limit |
UEFI Deeper Dive
There’s a lot to like about UEFI, but some complications do exist. Admins who want to install or dual boot Linux on existing Windows PCs may face obstacles. For one thing, UEFI’s Secure Boot functionality was designed to block execution of non-verified OS code. Also, there’s no way to upgrade older BIOS-equipped systems to UEFI. That means that implementing something like Secure Boot across the enterprise requires the physical replacement of older equipment.
The good news: UEFI offers a compatibility mode that interoperates with MBR-formatted hard drives and OSes lacking UEFI support. The UEFI CSM (Compatibility Support Module) emulates the legacy BIOS environment so newer PCs can support older hardware and OSes.
These types of large scale evolutions, while often slow to mature, can make a huge difference in the way we interact, customize, and troubleshoot hardware. With UEFI taking over as the standard in recent years, there’s a good chance you’ve already run across a system using it.
UEFI for Windows 11
Hopefully this blog cleared up the difference between a traditional BIOS and UEFI for you. If you would like to learn more about why UEFI is required for Windows 11, we’ve got a blog and video covering what you need to know.
We originally posted this blog on October 17, 2017. We updated this blog on March 18, 2022.
Get the Latest Tech Updates
Subscribe to our newsletters to get updates from OnLogic delivered straight to your inbox. News and insights from our team of experts are just a click away. Hit the button to head to our subscription page.
Share
More Articles
OnLogic Industrial Computers
Discover OnLogic's multitude of industrial computers that will help you to advance your IoT project
Learn more at OnLogic.com
OnLogic Industrial PCs: Designed to last. Built to order. Delivered in days. Visit our online store at OnLogic.com